随着.net 5在11月的发布,现在是谈论网络栈中许多改进的好时机。这包括对HTTP、套接字、与网络相关的安全性和其他网络通信的改进。在这篇文章中,我将重点介绍一些版本中更有影响力和更有趣的变化。
HTTP
更好的错误处理
自从.net 3.1发布以来,HTTP领域进行了许多改进和修复。当使用HttpClien时,最受关注的是添加如何区分超时和取消。最初,不得不使用自定义的CancellationToken区分超时和取消:
class Program{ private static readonly HttpClient _client = new HttpClient() { Timeout = TimeSpan.FromSeconds(10) }; static async Task Main() { var cts = new CancellationTokenSource(); try { // Pass in the token. using var response = await _client.GetAsync("http://localhost:5001/sleepFor?seconds=100", cts.Token); } // If the token has been canceled, it is not a timeout. catch (TaskCanceledException ex) when (cts.IsCancellationRequested) { // Handle cancellation. Console.WriteLine("Canceled: " + ex.Message); } catch (TaskCanceledException ex) { // Handle timeout. Console.WriteLine("Timed out: "+ ex.Message); } } }
这样做,客户端仍然抛出TaskCanceledException(为了兼容),但内部异常是超时时的TimeoutException:
class Program{ private static readonly HttpClient _client = new HttpClient() { Timeout = TimeSpan.FromSeconds(10) }; static async Task Main() { try { using var response = await _client.GetAsync("http://localhost:5001/sleepFor?seconds=100"); } // Filter by InnerException. catch (TaskCanceledException ex) when (ex.InnerException is TimeoutException) { // Handle timeout. Console.WriteLine("Timed out: "+ ex.Message); } catch (TaskCanceledException ex) { // Handle cancellation. Console.WriteLine("Canceled: " + ex.Message); } } }
另一个改进是将HttpStatusCode添加到HttpRequestException中。当响应上调用EnsureSuccessStatusCode时,新的StatusCode属性可以设置为空。然后,它可以在异常过滤器中使用:
class Program{ private static readonly HttpClient _client = new HttpClient(); static async Task Main() { try { using var response = await _client.GetAsync("https://localhost:5001/doesNotExists"); // The following line will throw HttpRequestException with StatusCode set if it wasn't 2xx. response.EnsureSuccessStatusCode(); } catch (HttpRequestException ex) when (ex.StatusCode == HttpStatusCode.NotFound) { // Handle 404 Console.WriteLine("Not found: " + ex.Message); } } }
由于HttpClient中方法:GetStringAsync, GetByteArrayAsync和GetStreamAsync不返回HttpResponseMessage,它们自己调用EnsureSuccessStatusCode。这些调用的异常过滤如下所示:
class Program{ private static readonly HttpClient _client = new HttpClient(); static async Task Main() { try { // The helper method will throw HttpRequestException with StatusCode set if it wasn't 2xx. using var stream = await _client.GetStreamAsync("https://localhost:5001/doesNotExists"); } catch (HttpRequestException ex) when (ex.StatusCode == HttpStatusCode.NotFound) { // Handle 404 Console.WriteLine("Not found: " + ex.Message); } } }
由于新的构造函数是public的,所以可以手动创建带有状态码的HttpRequestException:
class Program{ private static readonly HttpClient _client = new HttpClient(); static async Task Main() { try { using var response = await _client.GetAsync("https://localhost:5001/doesNotExists"); // Throw for anything higher than 400. if (response.StatusCode >= HttpStatusCode.BadRequest) { throw new HttpRequestException("Something went wrong", inner: null, response.StatusCode); } } catch (HttpRequestException ex) when (ex.StatusCode == HttpStatusCode.NotFound) { // Handle 404 Console.WriteLine("Not found: " + ex.Message); } } }
一致的跨平台实现
最初,.NET Core中的HTTP栈依赖于平台相关的处理程序:
- WinHttpHandler基于WinHTTP,适用于Windows。
- CurlHandler基于libcurl,适用于Linux和Mac。
由于两个库之间的差异,几乎不可能实现跨平台的一致性。因此,在.net Core 2.1中,我们引入了一个名为SocketsHttpHandler的托管HTTP实现。我们将大部分工作转移到SocketsHttpHandler,随着我们对它的可靠性越来越有信心,我们决定完全从System.Net.Http.dll中删除特定于平台的处理程序。在.net 5中,不再可能使用切换回System.Net.Http。然而,WinHttpHandler仍然作为一个独立的NuGet包可用。任何使用它的代码都需要更改为引用System.Net.Http.WinHttpHandler的NuGet包:
dotnet add package System.Net.Http.WinHttpHandler
并显式地向HttpClient构造函数传递WinHttpHandler实例:
class Program{ private static readonly HttpClient _client = new HttpClient(new WinHttpHandler()); static async Task Main() { using var response = await _client.GetAsync("http://localhost:5001/"); } }
SocketsHttpHandler扩展点
HttpClient是一个高级API,使用方便,但在某些情况下缺乏灵活性。在更高级的场景中,需要更精细的控制。我们试图弥合这些差距,并在SocketsHttpHandler中引入了两个扩展点——ConnectCallback和PlaintextStreamFilter。
ConnectCallback允许自定义创建新连接。每次打开一个新的TCP连接时都会调用它。回调可用于建立进程内传输、控制DNS解析、控制基础套接字的通用或特定于平台的选项,或者仅用于在新连接打开时通知。回调有以下注意事项:
- 传递给它的是确定远程端点的DnsEndPoint和发起创建连接的HttpRequestMessage。
- 由于SocketsHttpHandler提供了连接池,所创建的连接可以用于处理多个后续请求,而不仅仅是初始请求。
- 将返回一个新的流。
- 回调不应该尝试建立TLS会话。这是随后由SocketsHttpHandler处理的。
当不提供回调时的默认实现等价于以下最小的、基于套接字的回调:
private static async ValueTask<Stream> DefaultConnectAsync(SocketsHttpConnectionContext context, CancellationToken cancellationToken){ // The following socket constructor will create a dual-mode socket on systems where IPV6 is available. Socket socket = new Socket(SocketType.Stream, ProtocolType.Tcp); // Turn off Nagle's algorithm since it degrades performance in most HttpClient scenarios. socket.NoDelay = true; try { await socket.ConnectAsync(context.DnsEndPoint, cancellationToken).ConfigureAwait(false); // The stream should take the ownership of the underlying socket, // closing it when it's disposed. return new NetworkStream(socket, ownsSocket: true); } catch { socket.Dispose(); throw; } }
另一个扩展点,PlaintextStreamFilter,允许在新打开的连接上插入一个自定义层。在连接完全建立之后(包括用于安全连接的TLS握手),但在发送任何HTTP请求之前调用此回调。因此,可以使用它来监听通过安全连接发送的纯文本数据。这个回调的一般准则是:
- 它被传递一个流、协商的HTTP版本(可能与请求版本不同,参见ALPN)和初始化的HTTP请求。随后的请求也将使用相同的流。
- 流作为返回值。它可以是在没有任何更改的情况下传入的,也可以是封装它的自定义流。
如何实现自定义流可以在文档中找到。自定义流最终应该将读写任务委托给所提供的流,但它可以拦截交换的数据。
一个非常小的没有自定义流的PlaintextStreamFilter示例如下:
socketsHandler.PlaintextStreamFilter = (context, token) =>{ Console.WriteLine($"Request {context.InitialRequestMessage} --> negotiated version {context.NegotiatedHttpVersion}"); return ValueTask.FromResult(context.PlaintextStream); };
创建新扩展点连接的时间轴为:
- 调用ConnectCallback来打开TCP连接。
- 如果需要,SocketsHttpHandler内部建立TLS。
- 使用上一步中的流调用PlaintextStreamFilter。
如果没有注册回调函数,这里就不会调用任何东西。这两个回调函数都是为了对SocketsHttpHandler中的连接进行高级控制。应该非常小心地执行和测试它们,因为它们可能会无意中导致性能和稳定性问题。
HttpClient.Send的同步API
虽然我们建议使用异步网络API以获得更好的性能和可伸缩性,但我们也认识到,在某些情况下,使用同步API是必要的,并且会同步阻塞等待HttpClient。SendAsync经常有可伸缩性问题,因为需要多个线程来完成一个操作。这种方法的其他缺陷,包括臭名昭著的UI线程死锁。
为了启用同步场景并避免这些问题,我们添加了一个同步版本的HttpClient.Send,但是实现有一些注意事项:
- 仅支持HTTP/1.1协议。HTTP/2在共享连接上使用多路复用请求,因此交叉请求可能会被同步操作阻塞或阻塞。
- 它不能与前面提到的ConnectCallback一起使用。如果使用了默认SocketsHttpHandler以外的处理程序,它必须实现HttpMessageHandler.Send。否则,同步HttpMessageHandler.Send的默认实现将抛出。
- 类似的限制也适用于自定义HttpContent实现,它必须重写HttpContent.SerializeToStream,以便能够在同步调用中用作请求内容。
我们强烈建议尽可能继续使用异步api。
HTTP / 2
版本选择
这个特性是从支持明文HTTP/2 (h2c)的请求演变而来的。明文通信不仅适用于本地调试或测试环境,还可能存在防火墙或反向代理后的基于HTTP/2的服务,这些服务不使用TLS。例如,gRPC服务使用HTTP/2作为传输协议,有些服务选择放弃加密。
直到.net 5,一个不受支持的应用程序开关必须被打开才能启用明文HTTP/2通信,这可能会有问题,因为它不能启用每个请求控制。如果没有交换机,每个明文HTTP/2请求都会自动降级为HTTP/1.1。这是因为TLS扩展ALPN被用于与服务器协商最终的HTTP版本。没有TLS,因此没有ALPN,客户端不能确定服务器将能够处理HTTP/2。因此,客户端避免了风险,并选择了普遍支持的HTTP/1.1。但是,在前面提到的后端服务和gRPC的情况下,可能事先就知道所有参与者都可以处理h2c,因此自动降级是不可取的。
当我们设计版本选择时,我们试图概括原来的问题,并使API合理地“证明未来”。因此,我们决定让用户控制如何处理版本的降级和升级。我们引入了HttpVersionPolicy,这是一个新的enum,表示是否接受降级、升级,或者只接受准确的版本。用于手动创建并由HttpClient.SendAsync的发送。策略可以通过HttpRequestMessage.VersionPolicy直接设置到请求。对于GetAsync、PostAsync、DeleteAsync等在内部创建请求的调用,HttpClient实例属性HttpClient.DefaultVersionPolicy用于控制策略。
例如,要启用h2c场景,我们可以这样做:
class Program{ private static readonly HttpClient _client = new HttpClient() { // Allow only HTTP/2, no downgrades or upgrades. DefaultVersionPolicy = HttpVersionPolicy.RequestVersionExact, DefaultRequestVersion = HttpVersion.Version20 }; static async Task Main() { try { // Request clear-text http, no https. // The call will internally create a new request corresponding to: // new HttpRequestMessage(HttpMethod.Get, "http://localhost:5001/h2c") // { // Version = HttpVersion.Version20, // VersionPolicy = HttpVersionPolicy.RequestVersionExact // } using var response = await _client.GetAsync("http://localhost:5001/h2c"); } catch (HttpRequestException ex) { // Handle errors, including when h2c connection cannot be established. Console.WriteLine("Error: " + ex.Message); } } }
与HTTP/2的多个连接
HTTP/2允许多个并发请求一个TCP连接上的多路传输。根据HTTP/2规范,只应该向服务器打开一个TCP连接。这个建议对于浏览器非常有效,并且解决了HTTP/1打开每个源的多个连接的问题。然而,这将最大并发请求数减少到设置帧中的值,通常可以设置为100。对于服务到服务的通信,其中一个客户机向少量服务器发送非常多的请求,并且/或可以保持多个长期存在的请求,这一限制会显著影响吞吐量和性能。为了克服这个限制,我们引入了向单个端点打开多个HTTP/2连接的能力。
默认情况下,多个HTTP/2连接是禁用的。要启用它们,将SocketsHttpHandler.EnableMultipleHttp2Connections设置为true。
多个并发请求的示例如下:
class Program{ private static readonly HttpClient _client = new HttpClient(new SocketsHttpHandler() { // Enable multiple HTTP/2 connections. EnableMultipleHttp2Connections = true, // Log each newly created connection and create the connection the same way as it would be without the callback. ConnectCallback = async (context, token) => { Console.WriteLine( $"New connection to {context.DnsEndPoint} with request:{Environment.NewLine}{context.InitialRequestMessage}"); var socket = new Socket(SocketType.Stream, ProtocolType.Tcp) { NoDelay = true }; await socket.ConnectAsync(context.DnsEndPoint, token).ConfigureAwait(false); return new NetworkStream(socket, ownsSocket: true); }, }) { // Allow only HTTP/2, no downgrades or upgrades. DefaultVersionPolicy = HttpVersionPolicy.RequestVersionExact, DefaultRequestVersion = HttpVersion.Version20 }; static async Task Main() { // Burst send 2000 requests in parallel. var tasks = new Task[2000]; for (int i = 0; i < tasks.Length; ++i) { tasks[i] = _client.GetAsync("http://localhost:5001/"); } await Task.WhenAll(tasks); } }
控制台将显示来自ConnectCallback关于创建新连接的多条消息。如果将EnableMultipleHttp2Connections注释掉,控制台将只显示一条消息。
可配置的PING
HTTP/2规范定义了PING帧,这是一种确保空闲连接保持活跃的机制。此特性对于长时间运行的空闲连接非常有用,否则这些空闲连接将被删除。这样的连接可以在gRPC场景中找到,比如流和长时间的远程过程调用。到目前为止,我们只回复PING请求,从不发送。
在.net 5中,我们已经实现了发送PING帧的可配置间隔、超时,以及是否总是或仅在活动请求时发送它们。默认值的配置是:
public class SocketsHttpHandler{ ... // The client will send PING frames to the server if it hasn't receive any frame on the connection for this period of time. public TimeSpan KeepAlivePingDelay { get; set; } = Timeout.InfiniteTimeSpan; // The client will close the connection if it doesn't receive PING ACK frame within the timeout. public TimeSpan KeepAlivePingTimeout { get; set; } = TimeSpan.FromSeconds(20); // Whether the client will send PING frames only if there are any active streams on the connection or even if it's idle. public HttpKeepAlivePingPolicy KeepAlivePingPolicy { get; set; } = HttpKeepAlivePingPolicy.Always; ...}public enum HttpKeepAlivePingPolicy{ // PING frames are sent only if there are active streams on the connection. WithActiveRequests, // PING frames are sent regardless if there are any active streams or not. Always }
默认值KeepAlivePingDelay (Timeout.InfiniteTimeSpan)意味着该特性通常是关闭的,PING帧不会自动发送到服务器。客户端仍然会回复收到的PING帧,这是不能关闭的。为了启用自动PING, KeepAlivePingDelay必须更改,例如1分钟:
class Program{ private static readonly HttpClient _client = new HttpClient(new SocketsHttpHandler() { KeepAlivePingDelay = TimeSpan.FromSeconds(60) }); }
只有当与服务器没有主动通信时才发送PING帧。每一个来自服务器的传入帧都将重置延迟,只有在KeepAlivePingDelay没有接收到帧之后,才会发送一个PING帧。然后,服务器被给予KeepAlivePingTimeout应答时间间隔。如果没有,则认为连接丢失并被拆除。该算法会定期检查延迟和超时,但最多每秒钟检查一次。将KeepAlivePingDelay或KeepAlivePingTimeout设置为更小的值将导致异常。
例如,设置如下:
new SocketsHttpHandler(){ KeepAlivePingDelay = TimeSpan.FromSeconds(15), KeepAlivePingTimeout = TimeSpan.FromSeconds(7.5) };
将导致1.875秒间隔,因为它是两个值的1/4,即min(KeepAlivePingDelay, KeepAlivePingTimeout)/4。在这种情况下,超时可能发生在发送PING帧后的7.5到9.5秒之间。注意,检查间隔的计算是一个实现细节,将来可能会更改。
HTTP / 3
HTTP/3及其底层传输层QUIC正处于标准化的最后阶段。QUIC是一种新的基于udp的传输,与基于TCP的连接相比,它提供了一些好处:
-TLS安全链接握手更快
-在单个连接上更可靠的多路复用多个请求,消除了当数据包被丢弃时线路阻塞问题。
-连接迁移使移动客户端网络之间的转换更加流畅,例如Wi-Fi到LTE再返回。
. net 5引入了对HTTP/3的实验性支持——目前还不建议在生产环境中使用该特性。在底层,我们使用的是MsQuic库,它是一个开源的、跨平台的QUIC协议实现。如何使用QUIC启用HTTP/3的详细说明可以在System.Net.Experimental.MsQuic中找到。
- 目前,它只在内部构建的Windows上可用,这有QUIC所需的通道支持。
- 需要引用包含MsQuic库的包,该库目前仅通过实验性可用。
- HttpClient QUIC支持必须通过AppContext开关或DOTNET_SYSTEM_NET_HTTP_SOCKETSHTTPHANDLER_HTTP3DRAFTSUPPORT环境变量来启用,例如:
AppContext.SetSwitch("System.Net.SocketsHttpHandler.Http3DraftSupport", true);
- 请求必须有如下设置的Version和VersionPolicy属性:
new HttpRequestMessage{ // Request HTTP/3 version. Version = new Version(3, 0), // Only HTTP/3 is allowed, no version downgrades should happen. VersionPolicy = HttpVersionPolicy.RequestVersionExact }
这个设置告诉HttpClient我们已经预先知道了服务器支持HTTP/3并请求它。如果不支持HTTP/3,则会抛出异常。另一种选择是让服务器通过Alt-Svc报头发布HTTP/3。然后客户端可以将其用于后续请求。对于这个场景,请求不应该要求RequestVersionExact,因为它需要用较低的协议版本处理第一个请求。
更好的取消支持
基于Task的异步方法现在是异步编程的首选模式。它们在需要进行大量I/O操作的网络中特别有价值。Task模式使代码比原来的开始/结束“APM”模式更容易理解。基于Task的异步模式的一部分是使用CancellationToken来取消和超时。我们一直在努力添加取消令牌,并将其正确地应用到各个地方。我们仍然有遗漏重载的漏洞,但我们已经在.net 5中填补了许多。
对于socket,我们在SocketTaskExtensions中添加了重载——我们想在.net 6中将它们放Socket类本身中。使用CancellationToken的新重载如下:
public static class SocketTaskExtensions{ public static ValueTask ConnectAsync(this Socket socket, EndPoint remoteEP, CancellationToken cancellationToken); public static ValueTask ConnectAsync(this Socket socket, IPAddress address, int port, CancellationToken cancellationToken); public static ValueTask ConnectAsync(this Socket socket, IPAddress[] addresses, int port, CancellationToken cancellationToken); public static ValueTask ConnectAsync(this Socket socket, string host, int port, CancellationToken cancellationToken); }
这些重载已经在HttpClient和TcpClient中使用,导致了TcpClient中的新的重载:
public class TcpClient{ public ValueTask ConnectAsync(IPAddress address, int port, CancellationToken cancellationToken); public ValueTask ConnectAsync(IPAddress[] addresses, int port, CancellationToken cancellationToken); public ValueTask ConnectAsync(string host, int port, CancellationToken cancellationToken); }
在HTTP命名空间中,我们添加了HttpClient 和HttpContent 的重载。’ HttpClient ‘被扩展为’ Get(ByteArray|Stream|String)Async ‘重载:
class HttpClient{ public Task<byte[]> GetByteArrayAsync(string requestUri, CancellationToken cancellationToken); public Task<byte[]> GetByteArrayAsync(Uri requestUri, CancellationToken cancellationToken); public Task<Stream> GetStreamAsync(string requestUri, CancellationToken cancellationToken); public Task<Stream> GetStreamAsync(Uri requestUri, CancellationToken cancellationToken); public Task<string> GetStringAsync(string requestUri, CancellationToken cancellationToken); public Task<string> GetStringAsync(Uri requestUri, CancellationToken cancellationToken); }
HttpContent添加了序列化和读取的重载:
class HttpContent{ public Task<byte[]> ReadAsByteArrayAsync(CancellationToken cancellationToken); public Task<Stream> ReadAsStreamAsync(CancellationToken cancellationToken); public Task<string> ReadAsStringAsync(CancellationToken cancellationToken); protected virtual Task<Stream> CreateContentReadStreamAsync(CancellationToken cancellationToken); protected virtual Task SerializeToStreamAsync(Stream stream, TransportContext context, CancellationToken cancellationToken); public Task CopyToAsync(Stream stream, CancellationToken cancellationToken); public Task CopyToAsync(Stream stream, TransportContext context, CancellationToken cancellationToken); }
如果我们现在设计HttpContent,使用所有重载,我们将使CreateContentReadStreamAsync和SerializeToStreamAsync变为abstract 而不是virtual。问题是我们试图不通过改变公共类的契约来破坏现有的代码。在.net Core 3.1下运行的内容应该继续在.net 5下运行,没有任何改变。添加abstract 方法违背了这一承诺,所以我们不得不求助于virtual方法。自定义HttpContent实现应该重写它们,尽管它们只是virtual。所有HttpContent实现,比如byteraycontent、MultipartContent和StreamContent,都已经这样做了。
网络遥测
我们已经意识到,用户关于监视.net Core应用程序的内部网络描述并不好。到目前为止,只能收集非常详细且不一致的日志消息,侦听它们对性能有影响。对于.net 5,我们设计并实现了一套新的遥测事件和计数器。这些事件和计数器是在考虑持续监视的情况下创建的,因此它们不像内部日志那样占用大量资源。然而,它们并不是完全没有代价的,监听会消耗一些(尽管很少)CPU周期。
我们正在公开这些新的遥测事件和计数器,它们将供.net用户使用。我们计划在未来支持它们,对它们的任何更改都将被视为突破性的更改。
遥测事件和计数器都基于EventSource。它们可以通过EventListener在进程内使用,也可以通过EventPipe通过dotnet-trace和dotnet-counters命令行工具在进程外使用。
自定义遥测事件
一种自定义遥测事件的方法是通过EventListener在进程中编程:
class Program{ private static readonly HttpClient _client = new HttpClient(); static async Task Main() { // Instantiate the listener which subscribes to the events. using var listener = new HttpEventListener(); // Send an HTTP request. using var response = await client.GetAsync("https://github.com/runtime"); }} internal sealed class HttpEventListener : EventListener{ // Constant necessary for attaching ActivityId to the events. public const EventKeywords TasksFlowActivityIds = (EventKeywords)0x80; protected override void OnEventSourceCreated(EventSource eventSource) { // List of event source names provided by networking in .NET 5. if (eventSource.Name == "System.Net.Http" || eventSource.Name == "System.Net.Sockets" || eventSource.Name == "System.Net.Security" || eventSource.Name == "System.Net.NameResolution") { EnableEvents(eventSource, EventLevel.LogAlways); } // Turn on ActivityId. else if (eventSource.Name == "System.Threading.Tasks.TplEventSource") { // Attach ActivityId to the events. EnableEvents(eventSource, EventLevel.LogAlways, TasksFlowActivityIds); } } protected override void OnEventWritten(EventWrittenEventArgs eventData) { var sb = new StringBuilder().Append($"{eventData.TimeStamp:HH:mm:ss.fffffff} {eventData.ActivityId}.{eventData.RelatedActivityId} {eventData.EventSource.Name}.{eventData.EventName}("); for (int i = 0; i < eventData.Payload?.Count; i++) { sb.Append(eventData.PayloadNames?[i]).Append(": ").Append(eventData.Payload[i]); if (i < eventData.Payload?.Count - 1) { sb.Append(", "); } } sb.Append(")"); Console.WriteLine(sb.ToString()); } }
这个小程序将产生如下的控制台日志:
19:16:42.5983845 00000011-0000-0000-0000-00005d729c59.00000000-0000-0000-0000-000000000000 System.Net.Http.RequestStart(scheme: https, host: github.com, port: 443, pathAndQuery: /runtime, versionMajor: 1, versionMinor: 1, versionPolicy: 0) 19:16:42.6247315 00001011-0000-0000-0000-00005d429c59.00000011-0000-0000-0000-00005d729c59 System.Net.NameResolution.ResolutionStart(hostNameOrAddress: github.com) 19:16:42.6797116 00001011-0000-0000-0000-00005d429c59.00000000-0000-0000-0000-000000000000 System.Net.NameResolution.ResolutionStop() 19:16:42.6806290 00002011-0000-0000-0000-00005d529c59.00000011-0000-0000-0000-00005d729c59 System.Net.Sockets.ConnectStart(address: InterNetworkV6:28:{1,187,0,0,0,0,0,0,0,0,0,0,0,0,0,0,255,255,140,82,121,3,0,0,0,0}) 19:16:42.7115980 00002011-0000-0000-0000-00005d529c59.00000000-0000-0000-0000-000000000000 System.Net.Sockets.ConnectStop() 19:16:42.7157362 00003011-0000-0000-0000-00005d229c59.00000011-0000-0000-0000-00005d729c59 System.Net.Security.HandshakeStart(isServer: False, targetHost: github.com) 19:16:42.8606049 00003011-0000-0000-0000-00005d229c59.00000000-0000-0000-0000-000000000000 System.Net.Security.HandshakeStop(protocol: 12288) 19:16:42.8624541 00000011-0000-0000-0000-00005d729c59.00000000-0000-0000-0000-000000000000 System.Net.Http.ConnectionEstablished(versionMajor: 1, versionMinor: 1) 19:16:42.8651762 00004011-0000-0000-0000-00005d329c59.00000011-0000-0000-0000-00005d729c59 System.Net.Http.RequestHeadersStart() 19:16:42.8658442 00004011-0000-0000-0000-00005d329c59.00000000-0000-0000-0000-000000000000 System.Net.Http.RequestHeadersStop() 19:16:42.8979467 00005011-0000-0000-0000-00005d029c59.00000011-0000-0000-0000-00005d729c59 System.Net.Http.ResponseHeadersStart() 19:16:42.9037560 00005011-0000-0000-0000-00005d029c59.00000000-0000-0000-0000-000000000000 System.Net.Http.ResponseHeadersStop() 19:16:42.9090497 00006011-0000-0000-0000-00005d129c59.00000011-0000-0000-0000-00005d729c59 System.Net.Http.ResponseContentStart() 19:16:43.1092912 00006011-0000-0000-0000-00005d129c59.00000000-0000-0000-0000-000000000000 System.Net.Http.ResponseContentStop() 19:16:43.1093326 00000011-0000-0000-0000-00005d729c59.00000000-0000-0000-0000-000000000000 System.Net.Http.RequestStop() 19:16:43.1109221 00000000-0000-0000-0000-000000000000.00000000-0000-0000-0000-000000000000 System.Net.Http.ConnectionClosed(versionMajor: 1, versionMinor: 1)
命名为*Start和*Stop的事件使用相同的ActivityId触发。这些事件具有特殊的意义并自动关联。它允许像PerfView这样的监视工具计算操作所消耗的时间,或将其他事件链接到父事件。
另一种方法是通过dotnet-trace进程之外:
class Program{ private static readonly HttpClient _client = new HttpClient(); static async Task Main() { // No listener needed but print the process ID and wait for a key press to start the request. Console.WriteLine(Environment.ProcessId); Console.ReadKey(); // Send an HTTP request. using var response = await client.GetAsync("https://github.com/runtime"); } }
# Name the source events from previous example as providers (--providers).# Set the output file name (-o).# Set the process ID (-p). dotnet trace collect --providers System.Net.Http,System.Net.Sockets,System.Net.Security,System.Net.NameResolution -o networking.nettrace -p 1234
计数器
计数器可以通过EventListener在进程中以编程方式使用:
class Program{ private static readonly HttpClient _client = new HttpClient(); static async Task Main() { // Instantiate the listener which subscribes to the events. using var listener = new HttpEventListener(); // Send an HTTP request. using var response = await client.GetAsync("https://github.com/runtime"); }} internal sealed class HttpEventListener : EventListener{ protected override void OnEventSourceCreated(EventSource eventSource) { // List of event source names provided by networking in .NET 5. if (eventSource.Name == "System.Net.Http" || eventSource.Name == "System.Net.Sockets" || eventSource.Name == "System.Net.Security" || eventSource.Name == "System.Net.NameResolution") { EnableEvents(eventSource, EventLevel.LogAlways, EventKeywords.All, new Dictionary<string, string>() { // These additional arguments will turn on counters monitoring with a reporting interval set to a half of a second. ["EventCounterIntervalSec"] = TimeSpan.FromSeconds(0.5).TotalSeconds.ToString() }); } } protected override void OnEventWritten(EventWrittenEventArgs eventData) { // It's a counter, parse the data properly. if (eventData.EventId == -1) { var sb = new StringBuilder().Append($"{eventData.TimeStamp:HH:mm:ss.fffffff} {eventData.EventSource.Name} "); var counterPayload = (IDictionary<string, object>)(eventData.Payload[0]); bool appendSeparator = false; foreach (var counterData in counterPayload) { if (appendSeparator) { sb.Append(", "); } sb.Append(counterData.Key).Append(": ").Append(counterData.Value); appendSeparator = true; } Console.WriteLine(sb.ToString()); } } }
控制台日志是这样的:
19:38:55.9452792 System.Net.Http Name: requests-started, DisplayName: Requests Started, Mean: 0, StandardDeviation: 0, Count: 1, Min: 0, Max: 0, IntervalSec: 0.0004773, Series: Interval=500, CounterType: Mean, Metadata: , DisplayUnits: 19:38:55.9487031 System.Net.Http Name: requests-started-rate, DisplayName: Requests Started Rate, DisplayRateTimeScale: 00:00:01, Increment: 1, IntervalSec: 0.0004773, Metadata: , Series: Interval=500, CounterType: Sum, DisplayUnits: 19:38:55.9487610 System.Net.Http Name: requests-failed, DisplayName: Requests Failed, Mean: 0, StandardDeviation: 0, Count: 1, Min: 0, Max: 0, IntervalSec: 0.0004773, Series: Interval=500, CounterType: Mean, Metadata: , DisplayUnits: 19:38:55.9487888 System.Net.Http Name: requests-failed-rate, DisplayName: Requests Failed Rate, DisplayRateTimeScale: 00:00:01, Increment: 0, IntervalSec: 0.0004773, Metadata: , Series: Interval=500, CounterType: Sum, DisplayUnits: 19:38:55.9488052 System.Net.Http Name: current-requests, DisplayName: Current Requests, Mean: 1, StandardDeviation: 0, Count: 1, Min: 1, Max: 1, IntervalSec: 0.0004773, Series: Interval=500, CounterType: Mean, Metadata: , DisplayUnits: 19:38:55.9488201 System.Net.Http Name: http11-connections-current-total, DisplayName: Current Http 1.1 Connections, Mean: 0, StandardDeviation: 0, Count: 1, Min: 0, Max: 0, IntervalSec: 0.0004773, Series: Interval=500, CounterType: Mean, Metadata: , DisplayUnits: 19:38:55.9488524 System.Net.Http Name: http20-connections-current-total, DisplayName: Current Http 2.0 Connections, Mean: 0, StandardDeviation: 0, Count: 1, Min: 0, Max: 0, IntervalSec: 0.0004773, Series: Interval=500, CounterType: Mean, Metadata: , DisplayUnits: 19:38:55.9490235 System.Net.Http Name: http11-requests-queue-duration, DisplayName: HTTP 1.1 Requests Queue Duration, Mean: 0, StandardDeviation: 0, Count: 0, Min: ∞, Max: -∞, IntervalSec: 0.0004773, Series: Interval=500, CounterType: Mean, Metadata: , DisplayUnits: ms 19:38:55.9494528 System.Net.Http Name: http20-requests-queue-duration, DisplayName: HTTP 2.0 Requests Queue Duration, Mean: 0, StandardDeviation: 0, Count: 0, Min: ∞, Max: -∞, IntervalSec: 0.0004773, Series: Interval=500, CounterType: Mean, Metadata: , DisplayUnits: ms 19:38:55.9643081 System.Net.Sockets Name: outgoing-connections-established, DisplayName: Outgoing Connections Established, Mean: 0, StandardDeviation: 0, Count: 1, Min: 0, Max: 0, IntervalSec: 7.64E-05, Series: Interval=500, CounterType: Mean, Metadata: , DisplayUnits: 19:38:55.9643725 System.Net.Sockets Name: incoming-connections-established, DisplayName: Incoming Connections Established, Mean: 0, StandardDeviation: 0, Count: 1, Min: 0, Max: 0, IntervalSec: 7.64E-05, Series: Interval=500, CounterType: Mean, Metadata: , DisplayUnits: 19:38:55.9644278 System.Net.Sockets Name: bytes-received, DisplayName: Bytes Received, Mean: 0, StandardDeviation: 0, Count: 1, Min: 0, Max: 0, IntervalSec: 7.64E-05, Series: Interval=500, CounterType: Mean, Metadata: , DisplayUnits: 19:38:55.9644685 System.Net.Sockets Name: bytes-sent, DisplayName: Bytes Sent, Mean: 0, StandardDeviation: 0, Count: 1, Min: 0, Max: 0, IntervalSec: 7.64E-05, Series: Interval=500, CounterType: Mean, Metadata: , DisplayUnits: 19:38:55.9644858 System.Net.Sockets Name: datagrams-received, DisplayName: Datagrams Received, Mean: 0, StandardDeviation: 0, Count: 1, Min: 0, Max: 0, IntervalSec: 7.64E-05, Series: Interval=500, CounterType: Mean, Metadata: , DisplayUnits: 19:38:55.9645243 System.Net.Sockets Name: datagrams-sent, DisplayName: Datagrams Sent, Mean: 0, StandardDeviation: 0, Count: 1, Min: 0, Max: 0, IntervalSec: 7.64E-05, Series: Interval=500, CounterType: Mean, Metadata: , DisplayUnits: 19:38:55.9662685 System.Net.NameResolution Name: dns-lookups-requested, DisplayName: DNS Lookups Requested, Mean: 0, StandardDeviation: 0, Count: 1, Min: 0, Max: 0, IntervalSec: 1.6E-05, Series: Interval=500, CounterType: Mean, Metadata: , DisplayUnits: 19:38:56.0093961 System.Net.Security Name: tls-handshake-rate, DisplayName: TLS handshakes completed, DisplayRateTimeScale: 00:00:01, Increment: 0, IntervalSec: 1.99E-05, Metadata: , Series: Interval=500, CounterType: Sum, DisplayUnits:
或进程外部的启动计数器:
# Name the source events from previous example as providers (--providers).# Set the process ID (-p). dotnet counters monitor System.Net.Http System.Net.Sockets System.Net.Security System.Net.NameResolution -p 1234
这将启动计数器监视,用实际值覆盖终端窗口,看起来类似:
[System.Net.Http] Current Http 1.1 Connections 1 Current Http 2.0 Connections 0 Current Requests 1 HTTP 1.1 Requests Queue Duration (ms) 0 HTTP 2.0 Requests Queue Duration (ms) 0 Requests Failed 0 Requests Failed Rate (Count / 1 sec) 0 Requests Started 8 Requests Started Rate (Count / 1 sec) 1 [System.Net.Sockets] Bytes Received 1,220,260 Bytes Sent 3,819 Datagrams Received 0 Datagrams Sent 0 Incoming Connections Established 0 Outgoing Connections Established 1 [System.Net.NameResolution] Average DNS Lookup Duration (ms) 0 DNS Lookups Requested 1 [System.Net.Security] All TLS Sessions Active 1 Current TLS handshakes 0 TLS 1.0 Handshake Duration (ms) 0 TLS 1.0 Sessions Active 0 TLS 1.1 Handshake Duration (ms) 0 TLS 1.1 Sessions Active 0 TLS 1.2 Handshake Duration (ms) 0 TLS 1.2 Sessions Active 0 TLS 1.3 Handshake Duration (ms) 0 TLS 1.3 Sessions Active 1 TLS Handshake Duration (ms) 0 TLS handshakes completed (Count / 1 sec) 0 Total TLS handshakes completed 1 Total TLS handshakes failed 0
安全
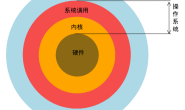
. net中的安全层依赖于底层操作系统及其功能。
-对于基于Linux的系统,我们使用OpenSSL,它从1.1.1版本起就支持TLS 1.3。
-对于Windows 10, TLS 1.3是可用的版本1903,但只用于测试目的,而不是生产。
此外,它是可选的,必须在注册表中启用。因此,TLS 1.3在之前的.net Core版本不能在Windows上工作。
这在内部预览版中有所改变,其中TLS 1.3是默认开启的,可以通过新的API使用。我们针对新的API调整了Windows上的SslStream实现,并在.net 5的Windows内部预览版本中对其进行了测试。
我们还追求在.net 5的SSL测试中获得A级。为了实现这一点,我们必须对Linux上的SslStream引入一个破坏性的更改,我们现在设置了一个被认为是强大的默认密码套件的自以为是的列表:
TLS 1.3 cipher suites TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384 TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256 TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384 TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256 TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256
然而,这些可以被多种方式重写:
- 在代码中,通过手动设置CipherSuitesPolicy或直接在调用SslStream.AuthenticateAs…方法。例如:
var sslStream = new SslStream(networkStream); await sslStream.AuthenticateAsClientAsync(new SslClientAuthenticationOptions(){ CipherSuitesPolicy = new CipherSuitesPolicy(new[] { TlsCipherSuite.TLS_AES_256_GCM_SHA384, TlsCipherSuite.TLS_CHACHA20_POLY1305_SHA256, TlsCipherSuite.TLS_AES_128_GCM_SHA256, TlsCipherSuite.TLS_AES_128_CCM_8_SHA256, TlsCipherSuite.TLS_AES_128_CCM_SHA256 }), });
- 或者通过 SocketsHttpHandler.SslOptions间接为HttpClient:
class Program{ private static readonly HttpClient _client = new HttpClient(new SocketsHttpHandler() { SslOptions = new SslClientAuthenticationOptions() { CipherSuitesPolicy = new CipherSuitesPolicy(new [] { TlsCipherSuite.TLS_AES_256_GCM_SHA384, TlsCipherSuite.TLS_CHACHA20_POLY1305_SHA256, TlsCipherSuite.TLS_AES_128_GCM_SHA256, TlsCipherSuite.TLS_AES_128_CCM_8_SHA256, TlsCipherSuite.TLS_AES_128_CCM_SHA256 }) } }; ...}
最后指出
本文并不是我们所做的所有更改的完整列表。如果你发现任何错误,请毫不犹豫地联系我们,你可以在dotnet/ncl别名下找到我们。
欢迎关注我的公众号,如果你有喜欢的外文技术文章,可以通过公众号留言推荐给我。

原文链接:https://devblogs.microsoft.com/dotnet/net-5-new-networking-improvements/